→ Настройка двухфакторной аутентификации в домене Astra Linux Directory |
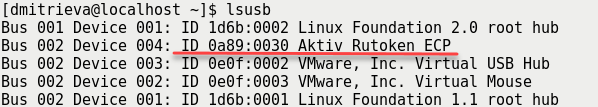
$ lsusb
В результате в окне Терминала отобразится название модели USB-токена:
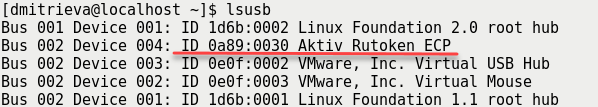
Убедитесь, что используете: Aktiv Rutoken ECP
Важно: время на клиенте и сервере должно быть синхронизировано. Невыполнение этого требования может привести к возникновению проблем. |
<username> = testuser<realm> = AKTIV-TEST<server> = aktiv-test.rukrb5-kdc, krb5-admin-server, krb5-pkinit AKTIV-TEST, доменное имя aktiv-test.ru (прописано в /etc/hosts на клиенте)testuser@AKTIV-TESTkrb5-user, krb5-config, krb5-pkinit AKTIV-TEST$ sudo apt-get install krb5-kdc krb5-admin-server krb5-pkinit # В диалогах указать: # realm = AKTIV-TEST # домен = aktiv-test.ru $ sudo krb5_newrealm # ввести пароль |
[domain_realm] .aktiv-test.ru = AKTIV-TEST aktiv-test.ru = AKTIV-TEST |
$ sudo kadmin.local # username = testuser # password = test kadmin.local:$ addprinc <username> # ... kadmin.local:$ quit |
$ kinit <username> ... $ klist ... $ kdestroy |
sudo apt-get install krb5-user libpam-krb5 libpam-ccreds auth-client-config krb5-pkinit opensc libengine-pkcs11-openssl # В диалогах указать: # realm = AKTIV-TEST # домен = aktiv-test.ru sudo dpkg-reconfigure krb5-config |
[domain_realm] .aktiv-test.ru = AKTIV-TEST aktiv-test.ru = AKTIV-TEST |
$ kinit <username> ... $ klist ... $ kdestroy |
$ openssl genrsa -out cakey.pem 2048 $ openssl req -key cakey.pem -new -x509 -out cacert.pem |
[ kdc_cert ]
basicConstraints=CA:FALSE
# Here are some examples of the usage of nsCertType. If it is omitted
keyUsage = nonRepudiation, digitalSignature, keyEncipherment, keyAgreement
#Pkinit EKU
extendedKeyUsage = 1.3.6.1.5.2.3.5
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
# Copy subject details
issuerAltName=issuer:copy
# Add id-pkinit-san (pkinit subjectAlternativeName)
subjectAltName=otherName:1.3.6.1.5.2.2;SEQUENCE:kdc_princ_name
[kdc_princ_name]
realm = EXP:0, GeneralString:${ENV::REALM}
principal_name = EXP:1, SEQUENCE:kdc_principal_seq
[kdc_principal_seq]
name_type = EXP:0, INTEGER:1
name_string = EXP:1, SEQUENCE:kdc_principals
[kdc_principals]
princ1 = GeneralString:krbtgt
princ2 = GeneralString:${ENV::REALM}
[ client_cert ]
# These extensions are added when 'ca' signs a request.
basicConstraints=CA:FALSE
keyUsage = digitalSignature, keyEncipherment, keyAgreement
extendedKeyUsage = 1.3.6.1.5.2.3.4
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer
subjectAltName=otherName:1.3.6.1.5.2.2;SEQUENCE:princ_name
# Copy subject details
issuerAltName=issuer:copy
[princ_name]
realm = EXP:0, GeneralString:${ENV::REALM}
principal_name = EXP:1, SEQUENCE:principal_seq
[principal_seq]
name_type = EXP:0, INTEGER:1
name_string = EXP:1, SEQUENCE:principals
[principals]
princ1 = GeneralString:${ENV::CLIENT} |
openssl genrsa -out kdckey.pem 2048 # создание запроса openssl req -new -out kdc.req -key kdckey.pem # подпись запроса REALM=<realm>; export REALM CLIENT=<server>; export CLIENT # содержимое файла pkinit_extensions выше openssl x509 -req -in kdc.req -CAkey cakey.pem -CA cacert.pem -out kdc.pem -extfile pkinit_extensions -extensions kdc_cert -CAcreateserial |
sudo mkdir /etc/krb5 sudo cp kdc.pem kdckey.pem cacert.pem /etc/krb5/ |
[realms]
AKTIV-TEST = {
database_name = /var/lib/krb5kdc/principal
admin_keytab = FILE:/etc/krb5kdc/kadm5.keytab
acl_file = /etc/krb5kdc/kadm5.acl
key_stash_file = /etc/krb5kdc/stash
max_life = 10h 0m 0s
max_renewable_life = 7d 0h 0m 0s
master_key_type = des3-hmac-sha1
supported_enctypes = aes256-cts:normal arcfour-hmac:normal des3-hmac-sha1:normal des-cbc-crc:normal des:normal des:v4 des:norealm des:onlyrealm des:afs3
default_principal_flags = +preauth
pkinit_anchors = FILE:/etc/krb5/cacert.pem
pkinit_identity = FILE:/etc/krb5/kdc.pem,/etc/krb5/kdckey.pem
} |
sudo kadmin.local kadmin.local$: modprinc +requires_preauth <username> |
# не забываем про ID! pkcs11-tool --module /usr/lib/librtpkcs11ecp.so --keypairgen --key-type rsa:2048 -l --id 45 openssl OpenSSL> engine dynamic -pre SO_PATH:/usr/lib/x86_64-linux-gnu/engines-1.1/pkcs11.so -pre ID:pkcs11 -pre LIST_ADD:1 -pre LOAD -pre MODULE_PATH:librtpkcs11ecp.so ... OpenSSL> req -engine pkcs11 -new -key 45 -keyform engine -out client.req -subj "/C=RU/ST=Moscow/L=Moscow/O=Aktiv/OU=dev/CN=testuser/emailAddress=testuser@mail.com" |
$ REALM=<realm>; export REALM $ CLIENT=<username>; export CLIENT $ openssl x509 -CAkey cakey.pem -CA cacert.pem -req -in client.req -extensions client_cert -extfile pkinit_extensions -out client.pem |
$ /etc/init.d/krb5-admin-server restart $ /etc/init.d/krb5-kdc restart |
pkcs11-tool --module /usr/lib/librtpkcs11ecp.so -l -y cert -w ./client.pem --id 45 sudo cp cacert.pem /etc/krb5/cacert.pem |
[libdefaults] default_realm = <realm> pkinit_anchors = FILE:/etc/krb5/cacert.pem # для аутентификации по локальному ключу # pkinit_identities = FILE:/etc/krb5/client.pem,/etc/krb5/clientkey.pem # для аутентификации по токену pkinit_identities = PKCS11:/usr/lib/librtpkcs11ecp.so |
$ kinit <username> |